, a twice yearly report that provides unique insights into the threat landscape to help organizations learn about trend data in industry vulnerabilities, exploits, malware and web-based attacks. The latest report identified Asia Pacific markets, especially the emerging ones, as among those at the highest risk of cybersecurity threats with three out of the top five global spots for rate of malware encounters in the region.
The new edition of the Microsoft Security Intelligence Report covers threat data from the first half of 2016, based on analysis of threat information from over a billion systems worldwide. Also included are longer term trend data and detailed threat profiles for over 100 individual markets and regions.
Out of the top five locations across the globe most at risk of infection, two are located in Southeast Asia, namely Vietnam and Indonesia. Both locations have a malware encounter rate of more than 45 percent in the second quarter of 2016, which is more than double the worldwide average of over 21 percent during the same period. The Philippines is #7 on the list with an encounter rates of 35.6%.
However, even markets in the region with higher levels of IT maturity such as Japan, Australia, New Zealand, South Korea, Hong Kong and Singapore have displayed malware enco
The report showed that the top most encountered malicious software families in the country include:
· Gamarue, a worm which can give a malicious hacker control of your PC, steal information and change PC security settings. It is commonly distributed via exploit kits and social engineering and can also be attached to spam mails.
· Lodbak, a trojan that is usually installed on removable drives by Gamarue, and which attempts to install Gamarue when the infected removable drive is connected to a computer; and Peals, which displays trojan characteristics.
Attackers also often use websites to conduct phishing attacks or distribute malware. Malicious websites typically appear completely legitimate and often provide no outward indicators of their malicious nature, even to experienced computer users. In many cases, these sites are legitimate websites that have been compromised by malware, SQL injection, or other techniques, in an effort by attackers to take advantage of the trust users have invested in them.
Based on the report, the Philippines has 5.99 drive-by download pages per 1,000 URLs compared to the worldwide number at 0.55. Drive-by downloads are malware or threats downloaded from the Internet which are usually unintentional. For example, downloading an executable program or movie file without knowing the malware attached.
Atty. Raul Cortez who leads Corporate, External and Legal Affairs (CELA) at Microsoft Philippines said, “With increasing malware encounters and sophistication of cyberattacks, cybersecurity is becoming a mission critical priority for most organizations. It generally takes an average up to 200 days for organizations to find out that they have been breached. With no sign of abatement in the future, what companies need is a Secure Modern Enterprise posture, which involves well-integrated “Protect-Detect-Respond” investments and capabilities, with a strategic focus on the core pillars – Identity, Apps, Data, Infrastructure and Devices. Additionally, organizations should also strongly consider adopting trusted cloud-based services to enjoy the highest levels of data protection, leveraging the cloud provider’s enterprise-grade security and privacy expertise, assurances and certifications.”
Security teams should also keep abreast of changes in the threat landscape brought about by emergence of cloud computing. The latest report contains an expanded Featured Intelligence section that includes a deep dive section on Protecting cloud infrastructure: detecting and mitigating threats using Azure Security Center. This section details new threats that organizations may encounter and explains how they can use Azure Security Center to protect, detect, and respond to security threats against Azure cloud-based resources. Some of the new
cloud-targeted threats outlined are:
· Pivot back attacks, which occurs when an attacker compromises a public cloud resource to obtain information that they then use to attack the resource provider’s on-premises environment
· “Man in the Cloud” attacks, in which an attacker induces a prospective victim to install a piece of malware using a typical mechanism, such as an email with a link to a malicious website. It then switches out the user’s cloud storage synchronization token with the attacker’s token, allowing the attacker to receive copies of each file the user places in cloud storage. This effectively makes the attacker a “man in the middle” for cloud storage.
· Side-channel attacks, where an attacker attempts to put a virtual machine on the same physical server as the intended victim. If he succeeds, the attacker will be able to launch local attacks against the victim. These attacks might include local DDoS, network sniffing, and man-in-the-middle attacks, all of which can be used to extract information.
· Resource ransom, where attackers hold cloud resource hostage by breaking into and controlling public cloud account,
and then requiring the victim to pay a ransom to release encrypted or restricted
resources.
Organizations need to ensure they have a robust cybersecurity posture to withstand and respond effectively to most cyberattacks and malware infections. Five best practices for improving defense against cybersecurity threats are:
· Ensure strong fundamentals: Use only genuine, current and updated software. The usage of IT assets which are old, unprotected, or are non-genuine in nature, substantially increase the chances for a cyberattack. For example, pirated and counterfeit software are known to come with embedded malware infections.
· Focus on cyber hygiene: Poor cyber hygiene of IT users, negligent employee behavior or weak credentials/password protection within an organization, adds a high degree of vulnerability for system compromise. With more and more personal devices being used at the workplace, the higher the chance they are infected.
· Have a data culture: Develop a big data analytics culture involving data classification, multifactor authentication, encryption, rights management, machine learning for behavioral analytics and log analytics to spot user anomalies and irregular or suspicious patterns, which could provide potential clues in advance to prevent impending or ongoing security breaches.
· Invest in a robust cyber defense ecosystem and monitor all systems in real time: Invest in trusted security solutions and modern threat protection technologies to monitor, detect and remove common and advanced cyber threats in real time, while developing in-house expertise to undertake threat analytics.
· Regular assessment, review and audit: Be comprehensive on all aspects of cybersecurity, not just technology. Have a IT trusted supply chain across cloud, software, hardware, Internet of Things, BYOD (bring your own device) and regularly review and assess cybersecurity investments and performance of both software and hardware deployment, including customer and vendor access to the corporate network.
Resources like the Security Intelligence Report are just one aspect of the Microsoft comprehensive approach to security – including a holistic platform, unique intelligence and broad partnerships – which is critical to enabling the digital transformation of leading organizations in Asia.
As part of Microsoft’s commitment to building trust in technology in the region, it launched its first combined
Transparency Center and Cybersecurity Center in October 2016. Located in Singapore, the joint facility brings together Microsoft capabilities in a single location in Asia Pacific, to serve the security needs of the public and private sector and foster the building of a trusted and secure computing environment.
To download and learn more about the Microsoft Security Intelligence Report findings, visit
www.microsoft.com/sir and the
Microsoft Secure Blog.




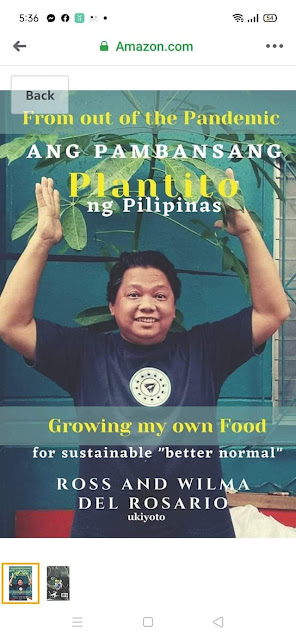
















 Ross is known as the Pambansang Blogger ng Pilipinas - An Information and Communication Technology (ICT) Professional by profession and a Social Media Evangelist by heart.
Ross is known as the Pambansang Blogger ng Pilipinas - An Information and Communication Technology (ICT) Professional by profession and a Social Media Evangelist by heart.











