Wazzup Pilipinas!
#LeniLeaks is a story about a traitor billionaire too busy plotting to #OustDuterte that she forgot to set their Yahoo Groups to private. Those Yahoo Group emails are damning. Medyo careless sila ano? Or talagang tanga lang? This is even worse than Clinton's. Who needs hackers...
Saturday, January 7, 2017
Friday, January 6, 2017
The Blue Palawan Kiteboard Open 2017

Wazzup Pilipinas!
Blue Kiteboarding and Blue Palawan Beach Club invites you to come and ride the worlds most tropical kite park this year!
The 2017 Blue Palawan Kite Open, the first International Slick and Slider Kiteboarding Competition in Puerto Princesa, Palawan, is back for it’s second year...
Kazunori Yokota Aims to Redeem Himself with Win Over Australian Foe

Wazzup Pilipinas!It is very rare for a debuting fighter to receive a title shot in his maiden fight under a particular mixed martial arts (MMA) organization’s banner, but this was the case when Japanese stalwart Kazunori Yokota made his first appearance in ONE Championship.Yokota was on ONE Championship’s...
Manila-Based Heavyweight Igor Subora Seeks Career Revitalization in Upcoming Bout

Wazzup Pilipinas!Ukrainian fighter Igor Subora sees his upcoming three-round encounter with Sherif “The Shark” Mohamed as an opportunity to bring back the luster of his professional mixed martial arts (MMA) career.Both highly-decorated combatants are set to collide on the undercard of ONE: QUEST...
History Asia To Premiere TV Special “President Obama: In His Own Words”

Wazzup Pilipinas!With the transition of power for the President of the United States of America to take place in a matter of days, HISTORY interrupts its regular programming to bring to Asia its two-hour TV special on the outgoing commander-in-chief, “President Obama: In His Own Words”.Reflecting...
#Traslacion2017: The Feast of Nuestro Padre Jesus Nazareno in Quiapo

Wazzup Pilipinas!#WalangPasok for all levels in the city of Manila on Monday, January 9, for the #Nazareno2017 . Devotees of the image of the #BlackNazarene will once again flock outside the Quiapo church. There will be tightened security, not only in Manila but nationwide, as the country will be...
Senator Tito Sotto Files Senate Resolution to Create Separate Film Festival for Indie Films

Wazzup Pilipinas!
"On a scale of 1 to Tito Sotto, how stupid are you?"
Senator Tito Sotto files Senate resolution creating a separate film festival for indie films, saying these shouldn't dominate the Metro Manila Film Festival (MMFF) every December.
Contrary to what he wants to happen,...
Mocha Uson Appointed as MTRCB Board Member

Wazzup Pilipinas!
"Why does this government keep trying to legitimize Mocha Uson? Why are they trying to repackage trash?" - Chowking Hazard @Watdahel_Marcel
Probably the BIGGEST JOKE I've heard from President Rodrigo Duterte ever! Mocha Uson has been appointed a board member of the Movie and...
Thursday, January 5, 2017
DOTr: Expect World-Class Air Traffic Service in the Philippines Very Soon

Wazzup Pilipinas!The Civil Aviation Authority of the Philippines (CAAP) under the Department of Transportation (DOTr) recently unveiled an early gift to Filipinos this Year-- the operationalization of the new Communications Navigation Surveillance / Air Traffic Management (CNS/ATM) system by end...
2017 Tech Predictions: Faster Speeds, Bigger Data, Smarter Cities

Wazzup Pilipinas!
Another year has come and gone, and we wonder about
what is forthcoming as citizens of a highly connected and digitized world. In a society where everything can change in
the blink of an eye, we list down what we think are most likely to happen in
the next dozen months.
LTE
Dominance
4G...
Burmese Countrymen Motivate Aung La N Sang to Win World Title

Wazzup Pilipinas!
Burmese mixed martial arts (MMA) superstar Aung La N Sang will have the opportunity of a lifetime as he gets a deserving shot at the ONE Middleweight World Championship belt.
Aung La challenges division kingpin Vitaly Bigdash in the main event of ONE: QUEST FOR POWER, which...
Privacy Commission Finds Bautista Criminally Liable for "ComeLeak" Data Breach

Wazzup Pilipinas!The National Privacy Commission (NPC) has found that the Commission on Elections (COMELEC) violated the Data Privacy Act of 2012; and has recommended the criminal prosecution of Chairman J. Andres D. Bautista, for the data breach that occurred between 20 and 27 of March last year.
In...
Eagerness to Win Keeps Vaughn Donayre Motivated in Upcoming Fight

Wazzup Pilipinas!When Vaughn Donayre directed his career path to ONE Championship nearly three years ago, he was once touted as a promising Filipino talent from the beautiful province of Cebu.However, the luster of his billing as a top-notch prospect slowly faded when a string of setbacks came his...
Wednesday, January 4, 2017
Once Upon a Mattress: An Explosion of Theatrical and Comedic Energy Set to Open on January 20

Wazzup Pilipinas!Ephesus Teatron Group, Inc. is all set to transport all of us to a magical world of musical theater as it proudly kicks off its first production for 2017 with “Once Upon a Mattress” at the Tanghalang Yaman Lahi Theater, Emilio Aguinaldo College located at 1221 Gen. Luna St. Ermita,...
DOE Pushes Simulations to Safeguard Consumers During Malampaya Scheduled Maintenance

Wazzup Pilipinas!Energy Secretary Alfonso G. Cusi pushes to firm up measures by each concerned agencies and power stakeholders during the course of the Malampaya maintenance repair from 28 January to 16 February 2017 to ensure readiness of all stakeholders and by way of ensuring consumers are protected...
NEC Automates Large-Scale Data Prediction for Business Systems

Wazzup Pilipinas!NEC Corporation announced the development of a “Predictive Analytics Automation Technology” that completely automates the process for large-scale data predictive analytics performed by relational databases that are widely used for business systems.Currently, when analyzing relational...
Power Restored to More Than 1 Million Households in Typhoon Nina-Affected Areas

Wazzup Pilipinas!With its 24/7 power restoration efforts, the energy family, spearheaded by the Department of Energy (DOE) together with its private institution partners, has resumed electricity supply to 1,003,519 households or about 57% re-energization of Typhoon Nina-affected areas as of 4 January...
Paws' Official Statement Regarding the Dog Killed in the MMFF Movie "Oro"

Wazzup Pilipinas!In the investigative meeting with the MMFF Executive Committe (the ORO team and the PAWS representatives were met by the MMFF ExeCom separately), several things were established:1. The ORO filmmakers lied to the MMFF Screening Committee. When the filmmakers were asked repeatedly...
Network Security in the Era of the Millennials

Wazzup Pilipinas!One of the toughest gigs in IT is the job of keeping an organization’s network safe. It is also one that is getting tougher with the rise of the millennial generation.Millennials - those in their 20s to mid-30s - are starting to dominate workplaces around the world. More than one-in-three...
DOH Thanks Everyone for Successful Anti-Firecracker Campaigns

Wazzup Pilipinas!“We would like to extend our gratitude for the support of other national agencies, the local government, non-government organizations, and the media during the anti-firecracker campaigns. Every year, we see the things that we need to strengthen in order to achieve our goal, and eventually,...
FDA Issues Cease and Desist Order vs Sanofi

Wazzup Pilipinas!The Philippine Food and Drug Administration (FDA) has issued a Summons with Cease and Desist Order against pharmaceutical giant Sanofi Pasteur Inc. for airing television and radio advertisements of its dengue vaccine, Dengvaxia. The airing of the advertisement is in violation of...
Subscribe to:
Posts (Atom)
Ang Pambansang Blog ng Pilipinas Wazzup Pilipinas and the Umalohokans.
Ang Pambansang Blog ng Pilipinas celebrating 10th year of online presence



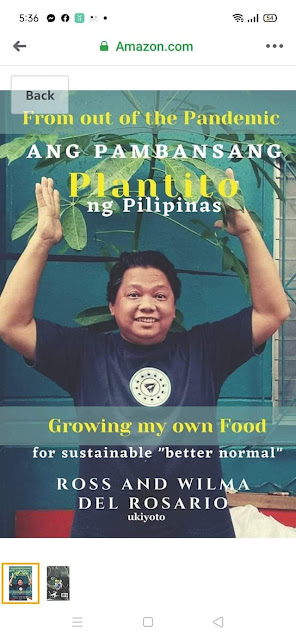




















 Ross is known as the Pambansang Blogger ng Pilipinas - An Information and Communication Technology (ICT) Professional by profession and a Social Media Evangelist by heart.
Ross is known as the Pambansang Blogger ng Pilipinas - An Information and Communication Technology (ICT) Professional by profession and a Social Media Evangelist by heart.






.jpg)




