Wazzup Pilipinas!
Ransomware has become the fastest growing malware
threat, targeting everyone from home users to healthcare systems to corporate
networks. Tracking analysis shows that there has been an average of more than
4,000 ransomware attacks every day since January 1, 2016.
On May 12, FortiGuard Labs began tracking a
new ransomware variant that spread rapidly throughout the day. It is a highly
virulent strain of a self-replicating ransomware that has impacted such
far-flung organizations as the Russian Interior Ministry, Chinese universities,
Hungarian and Spanish telcos, and hospitals and clinics run by the British
National Health Services. It is especially notable for its multi-language ransom
demands that support more than two-dozen languages.
This ransomware is being referred to by a number
of names, including WCry, WannaCry, WanaCrypt0r, WannaCrypt, or Wana Decrypt0r.
It is spread through an alleged NSA exploit called ETERNALBLUE that was leaked
online last month by the hacker group known as The Shadow Brokers. ETERNALBLUE
exploits a vulnerability in the Microsoft Server Message Block 1.0 (SMBv1)
protocol.
Note: More information below as well as in these
other related blogs.
Affected
Microsoft products include:
·
Windows
Vista
·
Windows
Server 2008
·
Windows 7
·
Windows
Server 2008 R2
·
Windows
8.1
·
Windows
Server 2012 and Windows Server 2012 R2
·
Windows
RT 8.1
·
Windows
10
·
Windows
Server 2016
·
Windows
Server Core installation option
Microsoft released a critical patch for this
vulnerability in March in Microsoft Security Bulletin MS17-010. That same month, Fortinet released an IPS signature to detect and block this
vulnerability. And we released new AV signatures today to also detect and stop
this attack. Third party testing also confirms that Fortinet Anti-Virus and
FortiSandbox effectively block this malware. Details about IPS and AV
signatures are included at the end of this article.
We
strongly advise all customers take the following steps:
• Apply the patch published by Microsoft on all affected nodes of the
network.
•
Ensure that the Fortinet AV and IPS inspections as well as web filtering
engines are turned on to prevent the malware from being downloaded, and to
ensure that web filtering is blocking communications back to the command and
control servers.
•
Isolate communication to UDP ports 137 / 138 and TCP ports 139 / 445.
We
also recommend that users and organizations take the following preventive
measures:
·
Establish
a regular routine for patching operating systems, software, and firmware on all
devices. For larger organizations with lots of deployed devices, consider
adopting a centralized patch management system.
·
Deploy
IPS, AV, and Web Filtering technologies, and keep them updated.
·
Back up
data regularly. Verify the integrity of those backups, encrypt them, and test
the restoration process to ensure it is working properly.
·
Scan all
incoming and outgoing emails to detect threats and filter executable files from
reaching end users.
·
Schedule
your anti-virus and anti-malware programs to automatically conduct regular
scans.
·
Disable
macro scripts in files transmitted via email. Consider using a tool like Office
Viewer to open attached Microsoft Office files rather than the Office suite of
applications.
·
Establish
a business continuity and incident response strategy and conduct regular
vulnerability assessments.
·
If
your organization has been affected by ransomware, here are some things to do:
·
Isolate
infected devices immediately by removing them from the network as soon as
possible to prevent ransomware from spreading to the network or shared drives.
·
If your
network has been infected, immediately disconnect all connected devices.
·
Power-off
affected devices that have not been completely corrupted. This may provide time
to clean and recover data, contain damage, and prevent conditions from
worsening.
·
Backed up
data should be stored offline. When an infection is detected, take backup
systems offline as well and scan backups to ensure they are free of malware.
·
Contact law
enforcement immediately to report any ransomware events and request assistance.
The
security of our customers’ systems is of paramount importance to Fortinet. We
are actively monitoring the situation to respond to any new malicious behavior
and will reach out immediately if new developments are discovered.
Solutions
IPS Signature:
MS.SMB.Server.SMB1.Trans2.Secondary.Handling.Code.Execution
AntiVirus signatures:
W32/Filecoder_WannaCryptor.B!tr
W32/WannaCryptor.B!tr
W32/Generic.AC.3EE509!tr
W32/GenKryptik.1C25!tr
CVE security
vulnerability database:
2017-0143
thru 2017-0148





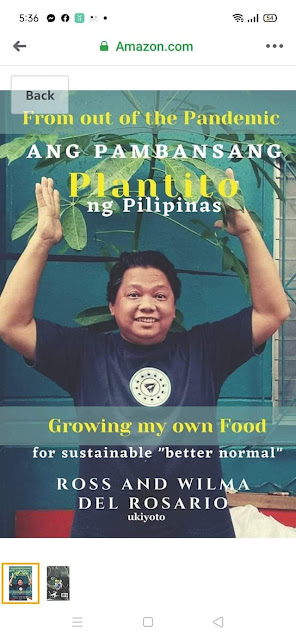




















 Ross is known as the Pambansang Blogger ng Pilipinas - An Information and Communication Technology (ICT) Professional by profession and a Social Media Evangelist by heart.
Ross is known as the Pambansang Blogger ng Pilipinas - An Information and Communication Technology (ICT) Professional by profession and a Social Media Evangelist by heart.







.jpg)




Post a Comment